Segment EU Alternative 2026: Twilio's CDP and the CLOUD Act — GDPR Risk for EU Customer Data Platforms
Post #936 in the sota.io EU Cyber Compliance Series | EU-ANALYTICS-SERIE Post #3
Segment is a Customer Data Platform — a category of software designed to collect user behavioral data from every touchpoint in your product, unify it into customer profiles, and route it to the analytics, marketing, CRM, and support tools your team uses. In 2020, Twilio acquired Segment for approximately $3.2 billion. Twilio Inc. is a Delaware corporation headquartered in San Francisco, California.
That corporate structure transforms what might seem like a European technical implementation detail — "we use Segment to route events" — into a multi-destination GDPR transfer problem. Every event your application sends to Segment, every customer identity that Segment unifies, and every destination that Segment feeds — Salesforce, Intercom, HubSpot, Amplitude, Customer.io, and 400+ others — passes through infrastructure owned by a company that is a US person under 18 U.S.C. § 2713, the Clarifying Lawful Overseas Use of Data Act.
The CLOUD Act allows US government authorities to compel Twilio to disclose electronic communications and records, regardless of where those records are stored. A Frankfurt data center hosting Segment events does not change Twilio's legal obligation to comply. The parent entity — a US person — can be served, and it must respond.
The consequence for EU product teams using Segment is not a minor compliance footnote. It is a structural GDPR violation under Articles 44-49 that five European data protection authorities have confirmed applies to this precise class of US-incorporated SaaS providers.
Segment's Architecture: Why the CDP Layer Multiplies Transfer Risk
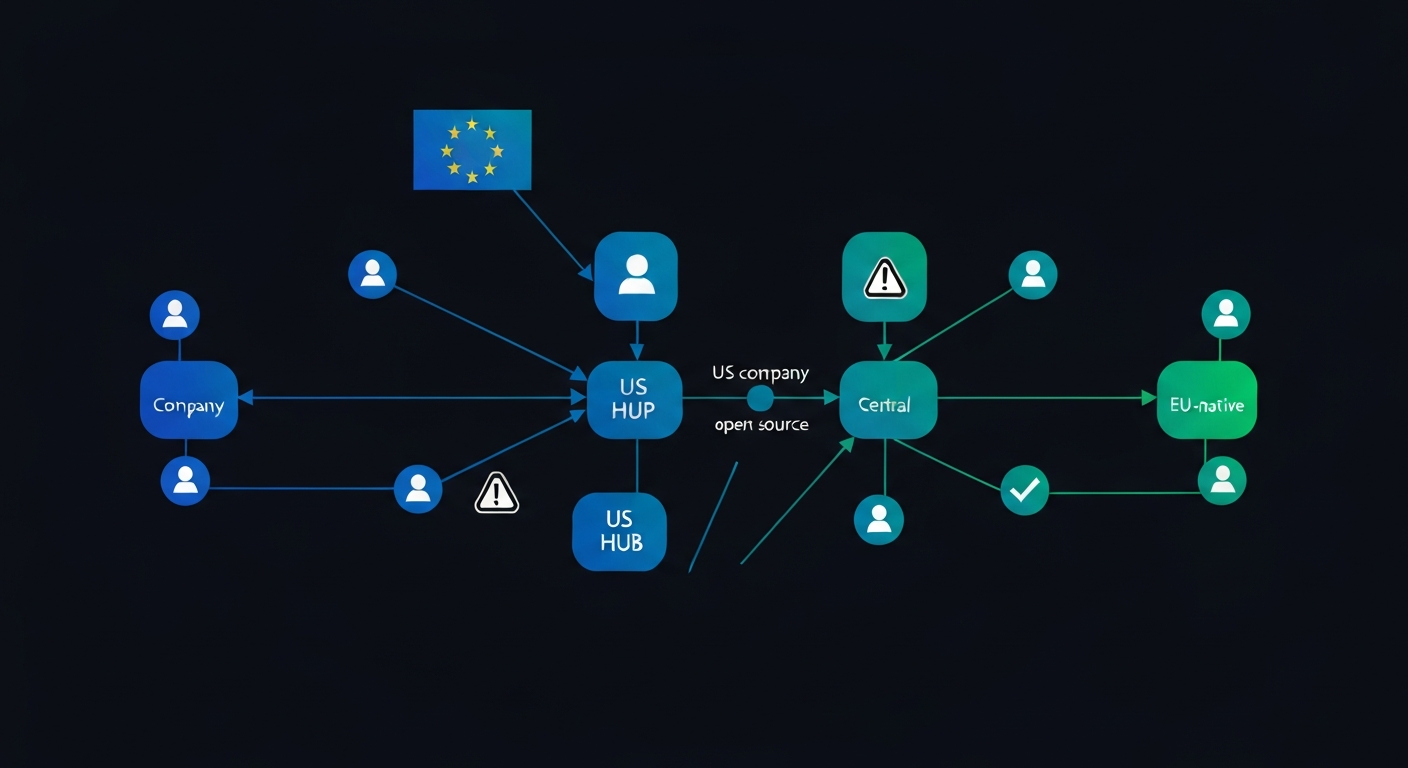
Most analytics transfer problems are point-to-point: your application sends data to Google Analytics, and Google Analytics creates the exposure. Segment introduces a different structure — a hub-and-spoke model in which every spoke represents a separate data transfer.
The Hub: Segment's Core Data Collection
Your application sends events to Segment's collection endpoint using the Analytics.js library, a server-side SDK, or a mobile SDK. Segment calls these "Sources." The basic payload includes:
Identity data. The userId — your internal identifier for the customer — and anonymousId — Segment's device-level identifier for unauthenticated users. For authenticated users, userId is typically the same value your database uses as the primary key for the user account. This alone constitutes personal data under GDPR Article 4(1).
Traits. Properties attached to a user identity: email address, name, company, plan tier, country, phone number. For B2B SaaS products, traits commonly include the customer's organization name, account ARR tier, and CRM owner. These are transmitted to Segment's servers on every identify() call.
Events and properties. Every tracked action in your product — Signup Completed, Feature Activated, Payment Processed, Subscription Upgraded — along with any properties you attach. Revenue figures, feature names, error messages, and user-provided content can all travel as event properties.
Group data. The group() call associates a user with an account or organization. B2B products commonly use this to pass company name, employee count, industry, and plan tier.
Page and screen context. URL, page title, referrer, viewport, IP address, user agent, and geographic location (derived from IP by Segment's servers).
All of this constitutes personal data under GDPR Article 4(1). The identity layer — email address linked to behavioral history — is arguably Special-category-adjacent for products in health, finance, or employment contexts, where behavioral patterns can reveal sensitive attributes.
The Spokes: Downstream Destination Transfers
This is where Segment's architecture creates a problem that is structurally worse than a single analytics tool.
Segment routes the collected data to Destinations — the tools in your marketing, analytics, and support stack. The current Segment destination catalog lists over 400 integrations. Common destinations for EU-facing SaaS products include:
- Salesforce (Salesforce, Inc. — Delaware corporation, San Francisco)
- HubSpot (HubSpot, Inc. — Delaware corporation, Cambridge, MA)
- Intercom (Intercom R&D Unlimited Company — Irish entity, but Intercom, Inc. is Delaware)
- Amplitude (Amplitude, Inc. — Delaware corporation, San Francisco)
- Customer.io (Peaberry Software, Inc. — Delaware corporation, Portland, OR)
- Mixpanel (Mixpanel, Inc. — Delaware corporation, San Francisco)
- Braze (Braze, Inc. — Delaware corporation, New York)
- Zendesk (Zendesk, Inc. — Delaware corporation, San Francisco)
Each of these destinations receives the same customer data that Segment collected. If you route userId, email, plan, and behavioral events to six destinations, you have created six separate international data transfers — each of which requires its own legal basis under GDPR Article 44.
For many EU SaaS products using Segment, the realistic destination count is 8-15 tools. Each tool is a US-incorporated company. The Segment layer acts as a transfer multiplier: one CLOUD Act-exposed SaaS hub routing to a dozen additional CLOUD Act-exposed SaaS spokes.
The Legal Chain: Why Twilio's Ownership Creates GDPR Exposure
Twilio Inc. as a US Person Under the CLOUD Act
The CLOUD Act (18 U.S.C. § 2713) imposes disclosure obligations on "providers of electronic communication service or remote computing service" that are under US jurisdiction. The key phrase: "regardless of whether such communication, record, or other information is located within or outside of the United States."
Twilio Inc. is incorporated in Delaware and headquartered in San Francisco. It is unambiguously a US person under the CLOUD Act. The company's 2020 Form 10-K filed with the SEC confirms its Delaware incorporation and US tax domicile.
Twilio's European entity — Twilio Ireland Limited — is a subsidiary that processes data on behalf of the parent. The CLOUD Act's reach is to the parent entity, which can be compelled to produce data held by its subsidiaries and affiliates globally. The Irish subsidiary's processing does not insulate the data from US government access requests directed at Twilio Inc.
Standard Contractual Clauses Do Not Eliminate CLOUD Act Risk
Twilio, like most US SaaS companies, offers Standard Contractual Clauses (SCCs) as the legal basis for international data transfers from the EU. SCCs are an Article 46 mechanism — "appropriate safeguards" that can form the legal basis for a transfer.
The problem identified by the Court of Justice of the European Union in its Schrems II judgment (Case C-311/18, July 2020) is that SCCs are a contractual instrument. They bind Twilio not to disclose data without legal basis. They do not and cannot bind the US government. When a National Security Letter, FISA § 702 order, or CLOUD Act demand arrives, Twilio's contractual commitment to EU data subjects is legally subordinate to US government access demands.
The Austrian Datenschutzbehörde's January 2022 analysis (which found Google Analytics unlawful) explicitly evaluated this point: supplementary technical measures — encryption, pseudonymisation — can potentially close gaps in data transfer legality, but only if the US entity never has access to the keys. For a SaaS tool that processes plaintext data to provide its core service, no supplementary technical measure can eliminate the CLOUD Act exposure. The service provider must be able to read the data to deliver the service.
Segment processes plaintext event data to route it to destinations. There is no architectural variant of Segment that could provide its core CDP functionality while simultaneously being unable to access customer data in response to a US government demand.
The EU-US Data Privacy Framework and Its Limitations
In July 2023, the European Commission adopted an adequacy decision for the EU-US Data Privacy Framework (DPF). Companies self-certifying under the DPF can use it as a transfer mechanism. Twilio has self-certified under the DPF.
However, the DPF's durability is uncertain. NOYB filed a legal challenge immediately after the Commission's adequacy decision. The challenge argues that FISA § 702 bulk surveillance — which the CJEU found incompatible with EU fundamental rights in Schrems II — has not been meaningfully reformed by the Intelligence Authorization Act for Fiscal Year 2024 or related US legislation. If the CJEU invalidates the DPF (as it invalidated Privacy Shield before it), transfers relying solely on the DPF will lose their legal basis retroactively from the date of invalidation.
Building your EU product's data infrastructure on a transfer mechanism that has twice been invalidated (Safe Harbor in 2015, Privacy Shield in 2020) and faces active legal challenge is not a sustainable compliance strategy.
What Data Segment Sends to Twilio's US Infrastructure
When your application calls analytics.identify(), analytics.track(), or analytics.page(), the following reaches Twilio's servers:
Identify calls. The full userId, any traits passed, and the anonymousId. For most SaaS products, an identify call after login contains: userId (your database ID), email, name, plan (subscription tier), company (for B2B), createdAt (account creation timestamp), and any custom traits you define. This is a rich personal data payload.
Track calls. The event name, event properties, userId, anonymousId, and automatic context: ip (full IP address before any anonymization), userAgent, locale, timezone, screen.width, screen.height, page.url, page.title, page.referrer, and page.search (which may contain URL parameters with PII). Revenue events pass revenue amounts. Ecommerce events pass product names, quantities, and prices.
Group calls. Company name, industry, employee count, plan tier, and any custom group traits. In B2B SaaS, this can effectively identify individual businesses.
Page calls. Full page URL, page title, referrer, and all automatic context fields. In multi-tenant SaaS, the URL path alone may reveal which account a user belongs to.
IP address. Unlike Google Analytics, Segment does not offer an IP anonymization option. The full client IP address is collected by Segment's servers as part of the network connection. This identifies the ISP, city, and often the specific office or residential address of the user.
Segment collects and routes all of this to Twilio's infrastructure, then forwards it to every destination you have configured. A single analytics.track("Payment Processed", { revenue: 299, plan: "enterprise" }) call may result in that payment data reaching Salesforce, HubSpot, Amplitude, Customer.io, and Slack simultaneously — each of which is a separate US-incorporated entity with its own CLOUD Act exposure.
Segment's EU Data Residency Option: What It Does and Does Not Fix
In 2022, Segment introduced an EU data residency option for Segment Connections. When enabled, customer data is stored and processed in Segment's Dublin, Ireland infrastructure rather than its US region.
This does not fix the GDPR transfer problem. The reasons are the same as for Google Analytics' EU data center option:
The CLOUD Act binds Twilio, not a data center. US government access demands are directed at Twilio Inc. as a US person. They compel the parent entity to produce records, regardless of which data center stores them. The Dublin infrastructure is operated by Twilio Ireland Limited, a wholly-owned subsidiary of Twilio Inc. A US government demand on Twilio Inc. can compel production of data held by its subsidiaries.
Not all destinations support EU residency. When Segment routes data to a destination, the data travels from Segment's Dublin infrastructure to the destination — which may itself be US-based. EU residency in Segment does not prevent data from reaching US-incorporated destinations like Salesforce or HubSpot.
EU residency is not available for all Segment products. Segment Engage (the audience builder and marketing automation product), Segment Protocols (schema governance), and some destination-specific features may not support EU data residency. A product team using the full Segment platform may find that only a subset of their data flows are covered.
SCCs and DPF concerns remain. Even with EU data residency enabled, Segment relies on SCCs or the DPF as the transfer mechanism. Both face the structural challenges described above.
EU data residency reduces the attack surface (data is stored in the EU and not routinely replicated to US servers) but does not eliminate the legal exposure created by Twilio's status as a US person.
EU-Native Alternatives to Segment
RudderStack (Open Source CDP)
RudderStack is an open-source Customer Data Platform with a self-hosted deployment option. The core product — RudderStack Open Source — can be deployed entirely on EU infrastructure you control: AWS eu-central-1 (Frankfurt), EU-based bare metal, or any EU-jurisdiction cloud provider.
Architecture. RudderStack uses the same source SDK model as Segment (Analytics.js-compatible sources, server-side SDKs, mobile SDKs). Events flow to your self-hosted RudderStack control plane and data plane, which you operate. Data never leaves your infrastructure until you route it to a destination.
GDPR relevance. A self-hosted RudderStack deployment eliminates the US-person intermediary entirely. Twilio does not handle your data. The CLOUD Act cannot reach your infrastructure because there is no US person involved in the data processing chain at the CDP layer.
Destinations. RudderStack supports 150+ destinations, including most tools in the Segment catalog. For destinations that are themselves US-incorporated (Salesforce, HubSpot), you still have transfer exposure for data sent to those destinations — but you have removed the CDP layer as an additional transfer point.
RudderStack Cloud. RudderStack also offers a managed cloud service. Rudderstack Inc. is a Delaware corporation. If you use RudderStack Cloud rather than the self-hosted version, the same CLOUD Act analysis that applies to Segment applies here.
EU-hosting recommendation. Deploy RudderStack Open Source on a single EU-jurisdiction VM. Resources: 2 vCPUs, 4 GB RAM handles most SaaS products at early growth stage. sota.io can host the RudderStack data plane alongside your application.
Jitsu (Open Source Event Collection)
Jitsu is an open-source event collection and streaming platform designed as a Segment alternative. It handles event ingestion, identity resolution, and routing to destinations.
Architecture. Jitsu uses a JavaScript SDK (compatible with existing Segment Analytics.js implementations) and a server-side ingest layer. Self-hosted on your infrastructure, it can be configured to route events directly to destinations without any US-person intermediary.
GDPR relevance. Self-hosted Jitsu operates entirely within the infrastructure you control. No third-party US entity processes the data. Jitsu Cloud (jitsu.com) is operated by Jitsu, Inc. — avoid the managed cloud option for GDPR compliance.
Destinations. Jitsu supports PostgreSQL, BigQuery, ClickHouse, Redshift, and 20+ other warehouses and streaming destinations. For direct SaaS tool routing (Salesforce, Intercom), native support is more limited than RudderStack.
Use case. Best for product teams whose primary need is warehousing event data for analytics, and who use a data warehouse (Snowflake, BigQuery, or a self-hosted ClickHouse) as the central analytics layer rather than routing events to many SaaS destinations.
mParticle (Enterprise CDP with EU Entity)
mParticle is an enterprise Customer Data Platform that offers a European data residency option through its EU cluster. Unlike Segment, mParticle's EU cluster routes data through mParticle's European infrastructure end-to-end.
GDPR relevance. mParticle's EU cluster reduces the US-person exposure compared to Segment's US-default routing. However, mParticle, Inc. is a Delaware corporation. The same CLOUD Act analysis applies: mParticle Inc. as a US person can be compelled to disclose records held by its European operations.
When to consider. For large enterprise teams that require a managed CDP and cannot operate a self-hosted RudderStack deployment, mParticle with EU residency reduces (but does not eliminate) the CLOUD Act exposure. It is a better compliance posture than Segment's default US region configuration.
Apache Kafka + dbt + ClickHouse (Data Stack Approach)
For product teams with engineering capacity, the fully EU-sovereign alternative is to build the CDP layer from GDPR-compliant components:
- Event collection: Self-hosted PostHog (Estonia entity, EU-native) or Jitsu for event ingest
- Event streaming: Apache Kafka on EU infrastructure for real-time event routing
- Identity resolution: Custom logic in dbt or a lightweight Python service
- Warehousing: ClickHouse or PostgreSQL on EU-jurisdiction infrastructure
- Activation: Direct API calls to destinations from EU infrastructure
This eliminates the US-person intermediary at the CDP layer entirely. The complexity cost is real — you own the infrastructure and the operational burden. But for products where EU data sovereignty is a core requirement (fintech, health, government-adjacent SaaS), it is the only option that fully eliminates the CLOUD Act transfer problem at the data collection layer.
Comparison: Segment vs. EU-Native Alternatives
| Tool | Jurisdiction | Self-Hostable | CLOUD Act Exposed | EU Data Residency | 400+ Destinations |
|---|---|---|---|---|---|
| Segment (Twilio) | Delaware, US | No | Yes | Partial | Yes |
| RudderStack Open Source | Self-hosted | Yes | No (self-hosted) | Full | 150+ |
| RudderStack Cloud | Delaware, US | — | Yes | No | 150+ |
| Jitsu Open Source | Self-hosted | Yes | No (self-hosted) | Full | 20+ |
| mParticle | Delaware, US | No | Yes (reduced) | Partial | 300+ |
| Apache Kafka stack | Your infra | Yes | No | Full | Custom |
Key insight: The only options that eliminate the CLOUD Act transfer problem at the CDP layer are self-hosted deployments. For teams that need a managed CDP, no US-incorporated vendor fully resolves the GDPR Art.44 transfer issue — they can only reduce it.
Practical Migration Path from Segment to RudderStack Open Source
Migrating from Segment to self-hosted RudderStack is the most common path for EU product teams addressing this compliance gap. The migration is less disruptive than it might appear.
Step 1: Deploy RudderStack on EU infrastructure. RudderStack Open Source requires two services: the control plane (UI and configuration) and the data plane (event processing). For most early-stage SaaS products, a single EU VM with Docker Compose handles both:
git clone https://github.com/rudderlabs/rudder-server
cd rudder-server
docker-compose up -d
The data plane exposes a write key-compatible API that accepts Segment-format events. No changes to your event structure are required.
Step 2: Update your write key. Replace the Segment write key in your Analytics.js or server-side SDK configuration with the RudderStack data plane URL and write key:
// Before (Segment)
analytics.load("YOUR_SEGMENT_WRITE_KEY");
// After (RudderStack)
analytics.load("YOUR_RUDDERSTACK_WRITE_KEY", "https://your-rudderstack.eu/v1/batch");
RudderStack's Analytics.js SDK is API-compatible with Segment's SDK. Most existing track(), identify(), page(), and group() calls work without modification.
Step 3: Reconnect destinations. In the RudderStack control plane, configure the same destinations you had in Segment. Note: each destination that is a US-incorporated entity (Salesforce, HubSpot, Intercom) remains a transfer point requiring its own GDPR legal basis. The RudderStack migration removes the Segment/Twilio transfer; it does not automatically fix transfers to US-incorporated destinations.
Step 4: Verify event parity. Run both Segment and RudderStack in parallel for 48-72 hours. Compare event volumes per destination to confirm parity before disabling Segment.
Step 5: Update privacy documentation. Remove Segment/Twilio from your privacy notice's list of data processors. Add RudderStack as self-operated infrastructure (not a third-party processor). Update your data processing records under GDPR Article 30.
The Destination Problem: Segment Removal Does Not Solve Everything
Removing Segment from your stack eliminates the CDP-layer CLOUD Act exposure. It does not eliminate transfer exposure created by the destinations themselves.
If your self-hosted RudderStack instance routes events to Salesforce (Delaware corporation), HubSpot (Delaware corporation), and Intercom (Delaware-registered US operations), you still have three international data transfers that require GDPR legal bases.
The DPF, SCCs, and EU data residency claims of each destination must be evaluated separately. For each destination that is a US-incorporated company, the same structural CLOUD Act analysis applies: the parent entity can be compelled to disclose data, regardless of where it is stored.
The most EU-sovereign architecture routes data exclusively to EU-headquartered or EU-regulated destinations:
- CRM: Pipedrive (Estonia, acquired by Vista Equity but operationally EU), Hubspot's German entity for EU customers (partial)
- Customer support: Crisp (France), Front (with EU-entity options)
- Email automation: Brevo (France, formerly Sendinblue), MailerLite (Lithuania)
- Product analytics: PostHog EU Cloud (Estonia/EU infrastructure) or Matomo self-hosted
A CDP routing to EU-native destinations throughout the stack eliminates CLOUD Act exposure at every layer. This is a significant architectural investment, but it is the only configuration that avoids systematic GDPR Art.44 violations across the entire customer data pipeline.
Implications for SaaS Architecture on EU Infrastructure
If you are building a product that processes EU personal data and uses a CDP layer, the GDPR-compliant path requires making explicit decisions at two levels:
At the collection layer: Choose between a self-hosted open-source CDP (RudderStack, Jitsu) that keeps data on EU infrastructure, or accept the ongoing CLOUD Act transfer exposure of using Segment, mParticle, or a similar US-incorporated managed CDP.
At the destination layer: For each tool in your destination catalog, evaluate whether it is a US-incorporated entity subject to the CLOUD Act. If it is, ensure you have a valid transfer mechanism and document the associated risks in your Records of Processing Activities (Article 30 RoPA).
On hosted EU infrastructure: For teams moving to EU-native infrastructure for this reason, hosting the RudderStack data plane on the same EU infrastructure as your application eliminates the need to route event data to any external service at the collection layer. The data plane can be a sidecar service alongside your application, adding no network latency and no US-person intermediary.
Data minimization: The CLOUD Act exposure scales with the volume and richness of data you collect. Segment's default SDK collects IP address, full URL path, user agent, and many automatic context fields. A more GDPR-aligned approach is to disable automatic context collection and pass only the specific properties your destinations need — reducing both the exposure surface and the personal data processing footprint.
Post #936 in the sota.io EU Cyber Compliance Series — EU-ANALYTICS-SERIE: Post #3 of 6.
EU-Native Hosting
Ready to move to EU-sovereign infrastructure?
sota.io is a German-hosted PaaS — no CLOUD Act exposure, no US jurisdiction, full GDPR compliance by design. Deploy your first app in minutes.