EU Identity Management Comparison 2026: Enterprise Buyer's Guide
Post #6 (Finale) in the sota.io EU Identity Management Series
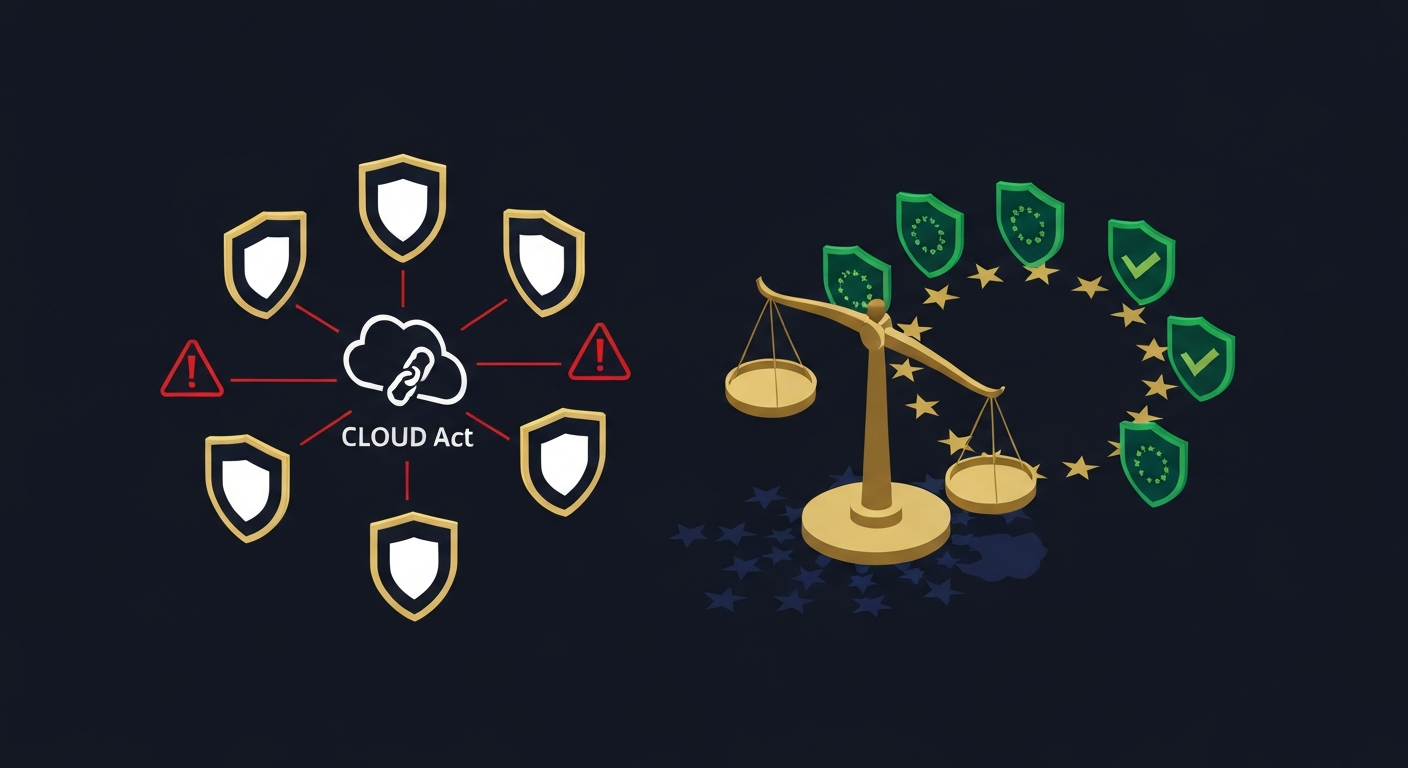
Identity and Access Management (IAM) is one of the most legally sensitive data categories an enterprise handles. Your IAM platform knows who has access to what, when, and from where — authentication logs, device trust metadata, multi-factor secrets, and federated identity tokens. If that platform is US-controlled, the CLOUD Act gives US authorities a direct subpoena path to your most critical access infrastructure.
Over the past five posts in this series, we've analyzed the five dominant US IAM platforms in depth — Microsoft Entra ID, Ping Identity, OneLogin, JumpCloud, and Duo Security. This finale synthesizes those findings into a decision framework for EU enterprise architects, compliance officers, and security teams evaluating IAM procurement or vendor review in 2026.
What This Series Found
All five platforms share a fundamental structural risk for EU enterprises: US parent company control. The CLOUD Act (Clarifying Lawful Overseas Use of Data Act, 2018) allows US authorities to compel US-incorporated companies to produce data held anywhere in the world, including EU data centers, even without EU court approval and often without notifying the data subject or the EU cloud provider.
| Platform | Corporate Parent | Jurisdiction | GDPR Risk Score | Notable Incident |
|---|---|---|---|---|
| Duo Security | Cisco Systems, Inc. | Delaware, USA | 22/25 | 2022 Yanluowang breach via Duo voice phishing |
| Microsoft Entra ID | Microsoft Corporation | Redmond, WA, USA | 20/25 | EU Digital Markets Act scrutiny, CLOUD Act exposure |
| OneLogin | One Identity LLC | Aliso Viejo, CA, USA | 20/25 | 2017 data breach, 2022 credential exposure incident |
| Ping Identity | Thoma Bravo (PE-owned) | Denver, CO, USA | 19/25 | Private equity ownership since 2022 |
| JumpCloud | JumpCloud, Inc. | Louisville, CO, USA | 19/25 | 2023 Lazarus Group nation-state breach |
The Duo Security Paradox
The highest GDPR risk score in this series (22/25) belongs to Duo Security — and the reason is deeply ironic. In 2022, the Yanluowang threat group (linked to Russian-speaking cybercriminals) breached Cisco's corporate network by voice-phishing an employee's Duo multi-factor authentication. The MFA platform used to protect corporate access was itself used as an attack vector. For EU enterprises running Duo as their MFA backbone, this means their authentication infrastructure has been demonstrably compromised — and remains under US CLOUD Act jurisdiction.
Duo's high score also reflects what it holds: TOTP secrets, device fingerprints, auth-event logs with IP and location data, and trusted-endpoint policy rules. That's the complete fingerprint of your workforce's access patterns.
GDPR Risk Score Breakdown: All Five Platforms
The five-axis GDPR risk matrix used throughout this series:
| Axis | Max | What We Measured |
|---|---|---|
| US Parent Corporation | 5 | CLOUD Act exposure, data center control, legal jurisdiction |
| Data Sensitivity | 5 | What the platform holds: auth tokens, secrets, user data |
| DORA/NIS2 Third-Party Risk | 5 | Critical infrastructure designation, concentration risk |
| EU Data Residency | 5 | Whether EU regions prevent CLOUD Act reach (spoiler: they don't) |
| Security Incidents | 5 | Documented breaches, CVEs, nation-state targeting |
Duo Security — 22/25
- US Parent Corp (5/5): Cisco Systems Inc., Delaware — one of the most comprehensive CLOUD Act exposures in enterprise software. Cisco is classified as a US telecommunications infrastructure company.
- Data Sensitivity (5/5): MFA secrets (TOTP seeds), authentication event logs, device trust metadata, push notification routing. These are the skeleton keys to your entire access infrastructure.
- DORA/NIS2 Third-Party Risk (4/5): For enterprises in financial services (DORA-regulated) or critical infrastructure (NIS2-regulated), Duo represents a tier-1 third-party concentration risk. A Duo outage blocks all MFA-protected access.
- EU Data Residency (4/5): Cisco offers EU-region deployment for Duo, but the US parent retains CLOUD Act authority regardless of where data is stored.
- Security Incidents (4/5): The 2022 Yanluowang breach is the clearest proof-of-concept that IAM platforms themselves are prime targets. Auth logs and device metadata were at risk.
Microsoft Entra ID — 20/25
- US Parent Corp (5/5): Microsoft Corporation — subject to CLOUD Act, FISA Section 702, PRISM program. EU regulators have repeatedly flagged Microsoft's data transfer practices (EU Schrems II fallout, EDPB recommendations on Microsoft 365 in public sector).
- Data Sensitivity (5/5): Entra ID holds your directory (all user identities), conditional access policies, MFA registrations, Azure AD tokens, and audit logs covering every authentication event across your Microsoft 365 ecosystem.
- DORA/NIS2 Third-Party Risk (4/5): As the identity backbone for the majority of EU enterprises, Entra ID represents extreme concentration risk. Many EU governments have banned or restricted Microsoft 365 for public sector use over exactly these concerns.
- EU Data Residency (3/5): Microsoft's EU Data Boundary commitment (since 2023) commits to storing and processing most EU customer data in the EU, but doesn't eliminate CLOUD Act reach for Microsoft as a US corporation.
- Security Incidents (3/5): 2023 Storm-0558 Chinese nation-state breach obtained Microsoft signing keys, enabling Entra ID token forgery. Microsoft's own security team admitted they could not fully trace the attack's lateral movement.
OneLogin — 20/25
- US Parent Corp (5/5): One Identity LLC, wholly owned by Francisco Partners (San Francisco-based PE firm). Multiple layers of US corporate control.
- Data Sensitivity (4/5): SSO tokens, SAML assertions, user directory, password vault. Notably, OneLogin includes a password manager component in enterprise tiers — increasing the sensitivity of what they hold.
- DORA/NIS2 Third-Party Risk (4/5): OneLogin is often deployed as the SSO layer for SaaS apps — a breach means session hijacking across your entire SaaS stack.
- EU Data Residency (4/5): EU-region option available. Same CLOUD Act caveat applies.
- Security Incidents (3/5): 2017 breach exposed encrypted passwords and multi-factor authentication phone numbers. 2022 credential exposure incident. Two significant security events in five years.
JumpCloud — 19/25
- US Parent Corp (5/5): JumpCloud Inc., Colorado incorporation. Raised $400M Series F in 2022 from US investors including SoftBank.
- Data Sensitivity (5/5): JumpCloud manages device identity, not just user identity. Directory + device MDM + SSH key management + VPN access = the broadest attack surface in this comparison.
- DORA/NIS2 Third-Party Risk (4/5): JumpCloud's device management scope means a compromise doesn't just expose credentials — it exposes physical endpoint inventory and SSH key material.
- EU Data Residency (3/5): No EU-region option at the same tier as Entra ID or Duo. Data processed in US regions by default.
- Security Incidents (2/5): 2023 Lazarus Group breach. North Korean state actors targeted JumpCloud specifically to reach downstream SaaS customers. Supply chain attack vector.
Ping Identity — 19/25
- US Parent Corp (5/5): Ping Identity Corporation, now owned by Thoma Bravo (Chicago-based PE firm). Private equity ownership since 2022 increases opacity around data handling decisions.
- Data Sensitivity (5/5): PingOne holds federated identity tokens, SAML assertions, OAuth tokens for enterprise applications, and user directory entries. Enterprise tier includes identity fraud detection data.
- DORA/NIS2 Third-Party Risk (4/5): Ping is the dominant IAM choice for tier-1 banks and financial services. A PingOne incident in a DORA-regulated firm triggers mandatory third-party incident reporting within 24 hours.
- EU Data Residency (3/5): EU-region option available for PingOne. Ping Identity Europe operates but parent company retains CLOUD Act exposure.
- Security Incidents (2/5): No major publicly disclosed breaches. PE ownership since 2022 means reduced transparency around security investments.
Feature Comparison Matrix
| Feature | Entra ID | Ping Identity | OneLogin | JumpCloud | Duo Security |
|---|---|---|---|---|---|
| SSO (SAML/OIDC) | ✅ Enterprise | ✅ Enterprise | ✅ Enterprise | ✅ Mid-market | ✅ Via Cisco SSO |
| MFA | ✅ Passwordless | ✅ FIDO2 | ✅ TOTP/Push | ✅ TOTP/Push | ✅ Best-in-class |
| Device Identity | ✅ Intune integration | ⚠️ Limited | ⚠️ Limited | ✅ Full MDM | ✅ Device Trust |
| SCIM Provisioning | ✅ | ✅ | ✅ | ✅ | ⚠️ Limited |
| B2B Federation | ✅ Azure B2B | ✅ | ⚠️ Limited | ⚠️ Limited | ❌ Not native |
| Passwordless | ✅ FIDO2 native | ✅ FIDO2 | ⚠️ Add-on | ⚠️ Beta | ✅ Push-based |
| On-premise option | ⚠️ ADFS (legacy) | ✅ PingFederate | ⚠️ Legacy | ❌ Cloud-only | ⚠️ Duo Auth Proxy |
| EU Data Region | ✅ (EU Data Boundary) | ✅ | ✅ | ⚠️ Limited | ✅ |
| GDPR Risk Score | 20/25 | 19/25 | 20/25 | 19/25 | 22/25 |
EU-Native Alternatives: The Full Map
If CLOUD Act exposure is a hard compliance blocker — as it increasingly is for public sector, critical infrastructure, and DORA/NIS2-regulated firms — here are the EU-native IAM platforms that emerged across this series:
Tier 1: Self-hosted, Zero US Exposure
Keycloak (Red Hat / IBM)
- Origin: Open-source, CNCF ecosystem, originally Red Hat (now IBM-owned)
- GDPR Risk: 3/25 (self-hosted = no external data transfer)
- Best for: Enterprises with Kubernetes infrastructure and in-house DevOps capability
- Strengths: Full SSO, SAML 2.0, OIDC, social login, admin API, SCIM support
- Weakness: Red Hat/IBM is still a US company — use community edition (not Red Hat SSO) for maximum sovereignty
- Deploy: Helm chart on self-managed Kubernetes, or dedicated VM
Authelia (Open Source, MIT License)
- Origin: Community-maintained, GitHub, no corporate parent
- GDPR Risk: 2/25 (open source, self-hosted, no telemetry)
- Best for: SME/startup with Docker/Kubernetes, reverse-proxy MFA gating
- Strengths: Extremely lightweight, works as an nginx/Traefik auth middleware, TOTP + WebAuthn
- Weakness: No enterprise support contract, no SCIM, limited SAML
Tier 2: European-headquartered Vendors
Zitadel (CAOS AG, Zürich, Switzerland)
- Origin: Swiss corporation, raised Series A from Swiss/European investors
- GDPR Risk: 5/25 (SaaS option = Swiss-hosted, GDPR-adequate country)
- Best for: Cloud-native enterprises wanting a managed IAM with European hosting
- Strengths: FIDO2 native, built on CockroachDB, excellent developer API, Terraform provider
- Note: Switzerland is GDPR-adequate, not EU, but has strong data protection via nFADP (2023)
WALLIX Authenticator (WALLIX Group SAS, Paris, France)
- Origin: French cybersecurity company, listed on Euronext Paris (WALX)
- GDPR Risk: 7/25 (French jurisdiction, EU headquarters, NIS2/DORA-native design)
- Best for: Enterprises in NIS2-regulated sectors (energy, finance, healthcare, transport)
- Strengths: MFA + PAM (Privileged Access Management) integration, native ANSSI certification support
- Note: WALLIX is primarily a PAM vendor — Authenticator is their MFA module, not a full IAM platform
Authentik (authentik Security GmbH, Berlin, Germany)
- Origin: German GmbH, open-core model, Goauthentik.io
- GDPR Risk: 4/25 (German entity, self-hosted option available)
- Best for: Mid-market enterprises wanting an open-core alternative to Okta/OneLogin
- Strengths: Beautiful admin UI, complete SSO/SAML/OIDC/LDAP, SCIM, proxy provider for legacy apps
Univention Corporate Server (Univention GmbH, Bremen, Germany)
- Origin: German GmbH, German public sector reference customer base
- GDPR Risk: 6/25 (German entity, self-hosted, LDAP/Kerberos-based)
- Best for: Organizations migrating from Active Directory, German public sector, education
- Strengths: Full AD replacement, group policy equivalent, native integration with German government IT
- Note: UCS 5.0 integrates Keycloak as the SSO layer
FreeIPA / Red Hat Identity Management
- Origin: Open-source (SSSD, MIT Kerberos, 389 Directory Server), Red Hat/IBM support option
- GDPR Risk: 3/25 (self-hosted open source)
- Best for: Linux-centric enterprises, Red Hat/CentOS/Fedora environments
- Strengths: Full directory + Kerberos + DNS + NTP + CA integration, no external SaaS dependency
Decision Framework: Which IAM Strategy Fits You?
Scenario A: "We Need CLOUD Act Zero" (Public Sector, Critical Infrastructure)
NIS2 Essential/Important Entity or DORA-regulated firm? Hard requirement: EU data sovereignty.
Recommended stack:
- Directory + SSO: Keycloak or Authentik (self-hosted, EU infrastructure)
- MFA: Authelia or Zitadel (Swiss-hosted acceptable if GDPR-adequate suffices)
- PAM for privileged access: WALLIX PAM Suite (French, ANSSI-certified)
- Device identity: FreeIPA or Univention (if Linux-heavy)
Scenario B: "We're EU but Have Microsoft 365 — What Do We Do?"
Microsoft Entra ID is deeply embedded in Microsoft 365. If you can't replace it immediately:
- Mitigate: Enable EU Data Boundary in tenant settings, audit guest account federation policies
- Complement: Deploy Keycloak as a second OIDC/SAML layer for non-Microsoft apps to reduce Entra ID's access footprint
- Long-term: Evaluate Authentik or Zitadel as a parallel identity directory for greenfield projects
Scenario C: "Our Board Wants a Plan but We're Practical"
If you're a mid-market EU company without a sovereign mandate, but want to reduce risk:
- Start with MFA: Replace Duo (22/25 risk) with Authelia or Zitadel MFA first. Lowest effort, highest risk reduction.
- Evaluate JumpCloud → FreeIPA/Keycloak migration for device identity (JumpCloud's 2023 Lazarus breach makes it a board-level risk).
- OneLogin → Authentik is a natural migration path for SSO/SAML apps.
Scenario D: "We're Under DORA Article 28 ICT Third-Party Risk"
DORA requires financial entities to maintain a Register of Information of all ICT third-party dependencies. Your IAM vendor appears in this register. Failure to manage concentration risk for critical functions is a DORA violation.
EU-native IAM reduces this concentration risk and simplifies your Register of Information (you control the software, not a US vendor with 30,000 EU customers potentially sharing the same platform outage).
EU Regulatory Snapshot for IAM in 2026
| Regulation | Applies To | IAM Implication |
|---|---|---|
| GDPR Art. 28 | All EU data controllers | IAM vendor is a data processor — DPA required |
| GDPR Chapter V | International transfers | CLOUD Act = potential unlawful transfer without SCCs |
| NIS2 Art. 21 | Essential + Important entities | IAM is a supply chain security risk — must be assessed |
| DORA Art. 28 | Financial sector ICT | IAM vendor in Register of Information, concentration risk rules |
| AI Act Art. 13 | AI systems using user data | Auth logs used for AI training = additional data protection layer |
| EUCS (planned) | EU cloud certification | Sovereign Level 3 would require EU-jurisdictional IAM |
The European Union Agency for Cybersecurity (ENISA) published its first IAM security baseline guidelines in 2025 (ENISA Guideline on Identity and Access Management for Cloud Services). The document explicitly flags US cloud providers' CLOUD Act exposure as a risk factor requiring documented risk acceptance from the data controller.
Total Cost of Ownership: Self-Hosted vs Managed EU
One objection to EU-native IAM is operational complexity. Fair. Here's a realistic TCO comparison for a 500-user enterprise:
| Platform | Licensing (Annual) | Hosting | Ops FTE (partial) | Total 3-Year |
|---|---|---|---|---|
| Entra ID P2 | €12,000 | Included | 0.2 FTE | ~€45,000 |
| Duo MFA (Advantage) | €18,000 | Included | 0.1 FTE | ~€55,000 |
| Keycloak (self-hosted) | €0 | €3,600/yr (2 VMs) | 0.3 FTE | ~€35,000 |
| Zitadel (managed, EU) | €6,000 | Included | 0.1 FTE | ~€22,000 |
| Authentik (self-hosted) | €0 | €3,600/yr | 0.3 FTE | ~€35,000 |
FTE cost assumed €120,000 fully loaded.
Zitadel's managed SaaS option emerges as the most cost-effective GDPR-compliant alternative — especially for organizations that want managed infrastructure without US data residency risk.
Migration Checklist: Moving from US IAM to EU-Native
Before migrating IAM platforms, your project team should complete these steps:
Phase 1 — Audit (2-4 weeks)
- Document all applications using your current IAM platform (SAML/OIDC/LDAP inventory)
- Map all user groups, roles, and conditional access policies
- Identify all MFA registrations and device trust policies
- Review current DPA with existing vendor
- Draft new DPA with EU-native vendor
Phase 2 — Parallel Run (4-8 weeks)
- Deploy EU-native platform in read-only mode alongside existing platform
- Migrate test user population to new platform
- Validate SAML assertions and OIDC tokens match expected format
- Test all application integrations against new IdP
Phase 3 — Cutover (2-4 weeks)
- Migrate all user MFA registrations (TOTP seeds cannot be transferred — users must re-enroll)
- Switch DNS/SAML endpoint references in each application
- Monitor authentication failure rates for 2 weeks post-cutover
- Decommission old IAM platform and terminate DPA
MFA Re-enrollment Note: TOTP seeds (the shared secrets behind Google Authenticator/Authy codes) are stored on the IAM platform side and cannot be exported in any of the five US platforms reviewed. Budget for a re-enrollment campaign — typically 2-3 weeks for a 500-person organization with an IT helpdesk available.
The Verdict: GDPR Risk Ranking
From highest to lowest CLOUD Act exposure risk for EU enterprises:
- 🔴 Duo Security (Cisco) — 22/25 — Replace immediately if NIS2/DORA-regulated. Voice phishing attack on your MFA infrastructure is a documented threat model, not a theoretical one.
- 🔴 Microsoft Entra ID — 20/25 — Acceptable for non-regulated enterprises with EU Data Boundary enabled. Hard to replace for Microsoft 365 shops. Plan a 3-year migration horizon.
- 🔴 OneLogin — 20/25 — Two documented breaches in five years. Migrate to Authentik or Zitadel.
- 🟡 Ping Identity — 19/25 — PE ownership opacity. DORA-regulated banks should request contractual CLOUD Act carve-outs. Long-term: evaluate EU-native.
- 🟡 JumpCloud — 19/25 — Nation-state breach in 2023. Device identity + SSH key exposure is highest-risk feature set. Migrate device management to FreeIPA or Univention.
If you're running EU-native hosting (Hetzner, OVH, Scaleway, sota.io) and concerned about IAM data sovereignty, the most pragmatic path forward in 2026 is:
- Immediate win: Deploy Keycloak or Authelia for new applications
- Medium-term: Migrate SSO layer to Authentik (best UI/UX of the self-hosted options)
- For managed SaaS: Zitadel (Swiss, GDPR-adequate, excellent FIDO2 support)
- For regulated sectors: WALLIX + Keycloak combination (French certification + open-source sovereignty)
This post is the sixth and final in our EU Identity Management Series. Previous posts: Microsoft Entra ID EU Alternative, Ping Identity EU Alternative, OneLogin EU Alternative, JumpCloud EU Alternative, Duo Security EU Alternative.
Hosting your applications on European infrastructure is the first step. Pairing EU hosting with EU-native IAM closes the data sovereignty loop. Explore sota.io's EU-native PaaS →
EU-Native Hosting
Ready to move to EU-sovereign infrastructure?
sota.io is a German-hosted PaaS — no CLOUD Act exposure, no US jurisdiction, full GDPR compliance by design. Deploy your first app in minutes.